Get your team alerted when specific events occur
Turn reporting events into actionable notifications so your team can respond fast and keep an audit trail.
Setup: connect reporting, then add webhook channels and rules to receive real-time alert payloads.
Stop watching dashboards. Start responding.
Alerting turns noisy security telemetry into the right message for the right channel, with filters that match how your team works.
Speed
Get notified in real time so triage starts immediately, not after someone notices.
Signal
Filter by directive, severity, origin, and event type to reduce alert fatigue.
Coordination
Route alerts to the tools your team already uses and keep an audit trail of notifications.
“We finally got the right reporting events into Slack actionable, not spam.”
Instant
Get alerted when something happens
How it works
Create notification channels, define rules, and send the right alerts when reporting events match your criteria.
- 1
Create channels
Create channels to receive alerts on Slack or by Webhook.
- 2
Define rules
Choose what should trigger: new origins, new scripts, hash changes, hash changes on wildcard URL patterns, or other key events.
- 3
Receive alerts
Receive alerts with enough detail to triage quickly and keep a record for reviews.
- 4
Respond with context
Take action based on the alert, correct SRI, ajust your CSP, keep track of the changes.
Script-inventory rule types
Four kinds of events can trigger alerts when Script Inventory is enabled. Each rule type focuses on a different change in the scripts your app loads.
New origin
Fires when scripts are loaded from a domain you weren't tracking before. Use it to catch new third-party or CDN sources as soon as they appear.
New script
Fires when a new script URL appears on an origin you already track. You get the URL and its hash so you can approve or investigate the new resource.
New hash
Fires when a script URL you monitor serves different content (hash changed). Same URL, new digest useful to detect tampering or unexpected updates.
New hash pattern
Fires when a script URL matching a wildcard pattern (for example `https://cdn.example.com/version-*.js`) serves a hash not seen before under that pattern scope.
Alert example
Webhook payloads (JSON) and how alerts look in Slack.
Webhook channel payloads
Example JSON sent to your webhook for each rule type.
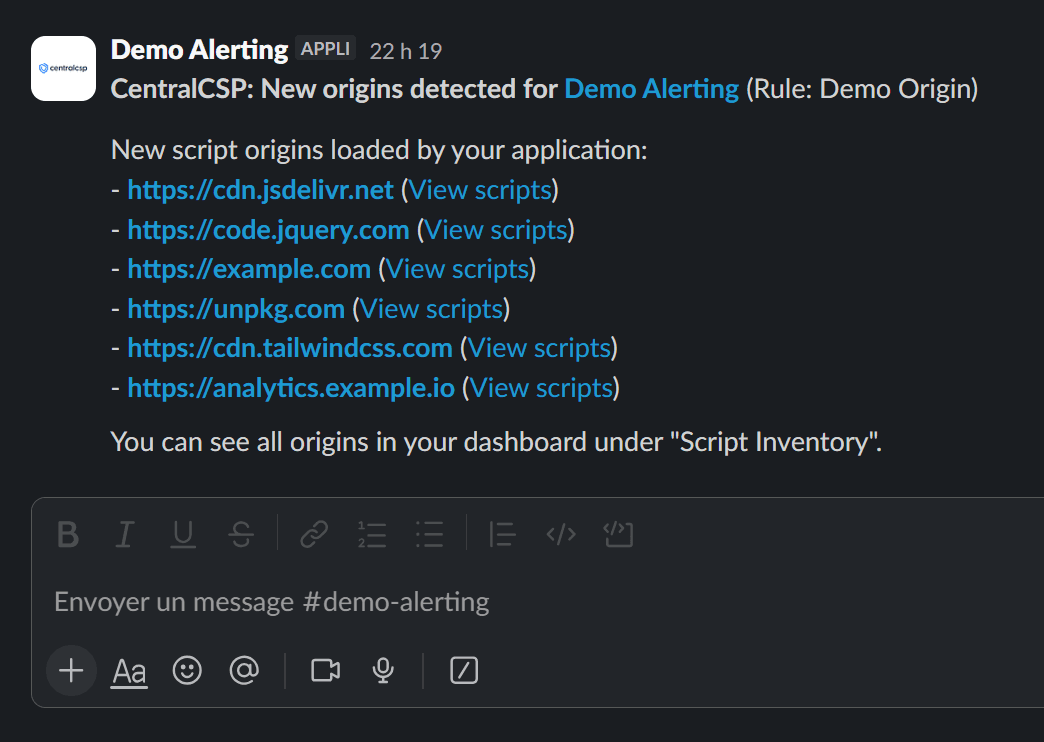
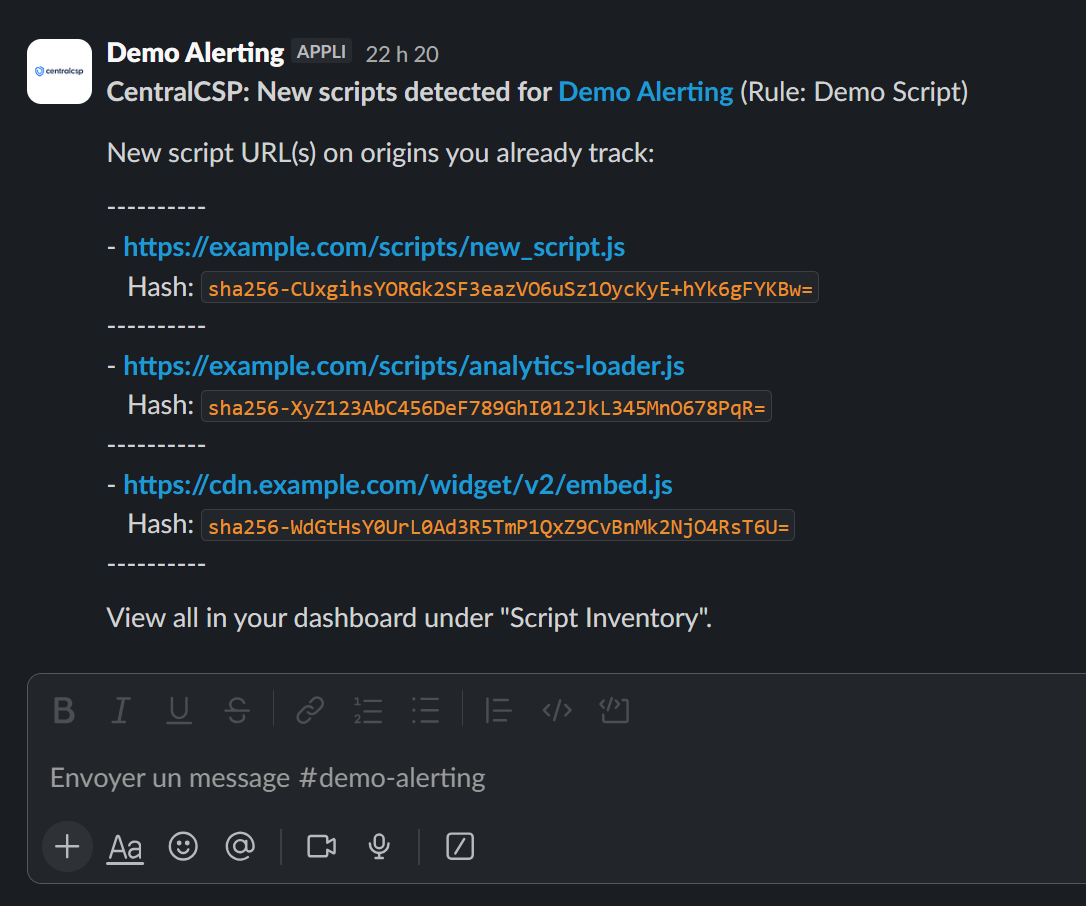
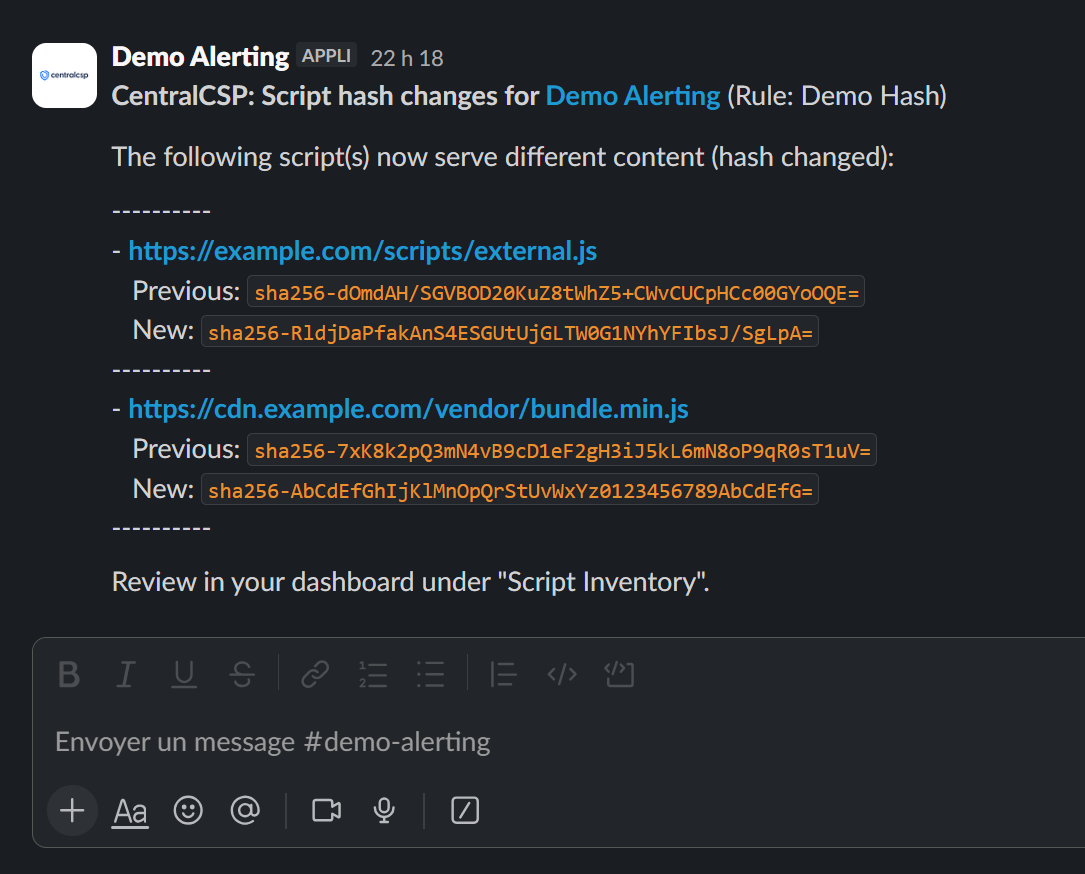
Slack
Alerts in Slack show rule name, summary, and a link to the event so your team can triage without leaving the channel.
How Alerting compares to the "Old Way"
Side-by-side: periodic dashboard checks vs. real-time notifications with filters.
| Metric | Manual / Legacy process | CentralCSP Alerting |
|---|---|---|
| Speed | Delayed. Someone has to notice the issue in the dashboard. | Real-time. Notifications arrive as soon as events occur. |
| Accuracy | Inconsistent. Different people triage differently and context gets lost. | Consistent. Rules and filters standardize what triggers and what's sent. |
| Visibility | Siloed. Events don't reach the right owners quickly. | Routed. Alerts go to specific channels and teams with an audit trail. |
| Effort | High. Lots of manual monitoring and follow-ups. | Low. Automate routing and focus humans on response. |
Frequently Asked Questions
Everything you need to know about Alerting
Additional Tools
Explore our comprehensive suite of tools designed to help you manage and optimize your Content Security Policy.
Monitor and analyze Content-Security-Policy violations in real-time
Automatically generate a tight policy for your website, based on your website's content.
Monitor all the scripts loaded on your website, their integrity hashes and known CVEs.
Monitor your payment pages for PCI DSS v4.0 compliance.
Get alerted on your favorite channels when a specific event occurs.
Ready to get alerted?
Set up channels and rules so you never miss important CSP or script-inventory events.